- Privacy may be a human right, but it’s not free. If you’re short on cash, save up before you go dark.
- According to J.J. Luna, the first thing to do is to separate your mailing address from your home address.
- Take advantage of privacy companies to mask phone calls, credit cards, email addresses and everything else you need to remain anonymous while transacting business and living life these days.
- When asked for ID, offer your passport. It’s good photo ID and accepted everywhere. It also doesn’t give away your home address.
This is Part 4 of a four-part article on PERSEC/Privacy. Please click here for Part 1, here for Part 2 and here for Part 3.
In part four of this series, I will address pattern of life and how it affects privacy, security and freedom.
Manage Your Pattern of Life (PoL) Relative to Privacy
Each of us has a pattern of life or PoL. Our PoL is the sum of our habits. In the context of privacy, every day, we make choices that impact the degree to which we are free from unwanted scrutiny, surveillance or disclosure of information that we consider sensitive. While privacy is a universal human right, it’s not free. Maintaining any degree of privacy has a cost in both dollars and convenience. I call it a cost, but I prefer to consider it an investment because it pays dividends in privacy, security and freedom.
Why should you manage your PoL? With enough information about your PoL, it is possible to predict your future actions, and the more information the persons doing the predicting have, the more accurate their predictions become.
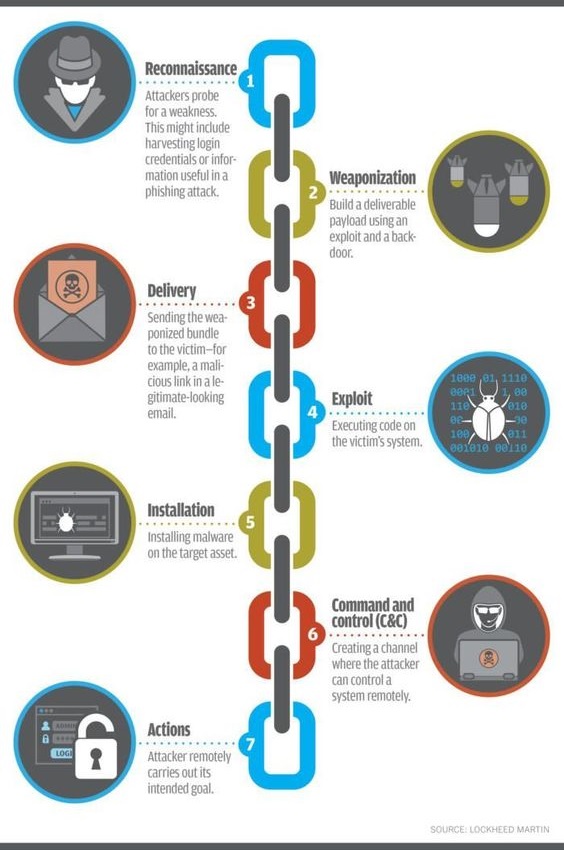
PoL data can come from credit or banking records, customer loyalty cards, camera systems that track pedestrians, automated license plate recognition systems and online behaviors. The NSA uses a database/analysis toolset called MARINA to track intercepted internet metadata. It tracks what users do as they browse the internet. It doesn’t matter if you are a US citizen either because US law doesn’t consider metadata to be data.
Pay in Cash or Barter
When it comes to tracking you down, little intelligence is more valuable than information about your spending habits.
Get in the habit of either bartering or paying in cash. Barter and cash are so fundamental to privacy that all over the world over, enemies of freedom are salivating at the prospect of cashless societies because they spell the end of freedom and total control over the populace.
Using bank cards and/or customer loyalty cards creates a paper trail that includes the location of the transaction, time and date, and a list of each item purchased. Using credit cards is even worse. to buy vehicles or real estate creates paper trail that makes it a cinch to find you. Convenient access to credit means young people now buy everything their parents amassed over the course of a lifetime in the first couple years after they leave home. This often saddles them with a mountain of debt and means that they pay for all that stuff many times over. Then they too often turn around and gripe about how they are “generation financially screwed” when they did it to themselves.
Rent until you can afford to buy or make do with less and you’ll be able to get by on less, become far richer and protect your privacy. Cars, firearms, homes, technology and other major purchase should be paid for in cash. Not owing a cent to anyone is liberating and means I don’t create nearly as much of a paper trail. I haven’t used a credit card in well over a decade and can honestly tell you that it is possible to live debt-free.
Paying in cash decreases the amount of paperwork required to do business, most of which stems from the fact that the other party is extending you credit. If you pay cash up front, there is no need for the vendor to extend credit to you and therefore no need to collect sensitive information. If a vendor won’t accept cash, find one who will.
Save for a Rainy Day
While most emergencies are far from catastrophic, 61% of Americans don’t have enough savings on hand to deal with a $1,000 emergency. Over the years, J.J. Luna has given out a lot of advice to privacy seekers. When he cited an example where a friend paid 6 months rent in advance in order to avoid giving out his SSN, he was asked for advice by a reader who could barely come up with a deposit and the first month’s rent. He told them to hold off on working on their privacy temporarily and forgo all unnecessary expenses until they had a minimum of $5,000 on hand and then start working on their privacy again.
This was sound advice, and not just concerning privacy. Most emergencies require a little money at some point. Unless you plan to disappear into the wilderness and never come out, attaining any considerable degree of privacy requires at least some savings.
Understand How PoL Makes You Easy to Find
Let’s say I need to get out of Dodge. Even small details that you might overlook can be huge clues. If you are not aware of them, they can get you caught, but if you are aware of them, you can use them to your advantage by leaving false clues or spreading disinformation.
Becoming untrackable is a process, not an event. Whoever is set on your trail is going to understand that and is going to know what you need to do in order to become untrackable. If logs at your ISP indicate that you have been reading a bunch of articles, swiss bank accounts and boning up on your Icelandic, whoever is looking for is going to have a pretty good idea of where to start looking.
I suppose, from that point of view, this type of tracking isn’t too different from counter-tracking because once you understand how the tracking party tracks a quarry, you can start using that to your advantage. Make sure that any books you buy off Amazon with a credit card are about chainsaws, cold weather survival and building log cabins in Canada before you take off to someplace tropical.
If your PoL includes season tickets, memberships, hobbies or religion, whoever is after you will use your passions to track you down. You should either drop them an find new hobbies or begin replacing them with misinformation online. For example, if someone tied my pen name to my legal name, they’d easily surmise that I’m passionate about emergency preparedness and survival. While the world is a big place, narrowing the search down to survivalists isn’t so daunting. Add in another hobby or two and the groups may have very little overlap. If you refuse to exchange your old passions for new ones, at least change them online.
Separate Your Residence from Your Mailing Address
Until you separate your home address from the address(s) where you receive mail and packages you remain easy to find. If you have lived in the same place for any length of time, registered the utilities in your own name and receive mail in your own name, finding you will be trivially easy for anybody who cares to.
If you are serious about your privacy, one of the best things you can do is to move. If your lifestyle allows, move often. This is easiest to do if you own your own business and don’t have any employees. Moving affords an opportunity to break with your past and become much harder to locate.
When you move …
- Open New Accounts – Either close out your accounts or nearly empty them. Open new accounts in the name of LLCs or nominees. See the book How To Be Invisible by J.J. Luna for more detailed information on both options.
- Get New Mailing Addresses – Receive mail through ghost addresses and PO Boxes or commercial mail forwarding agencies. There are pros and cons to each of these. I suggest using a box at a business, not a USPS post office. According to Frank M. Ahearn, author of How to Disappear, good a good skip tracer can fool a postal worker into revealing your information, but this seldom succeeds with businesses that rend PO Boxes because they could be held liable for disclosing your information, while you have little recourse against the USPS. JJ Luna suggests applying for a PO Box before you move and simply not reporting to UPSPS that you’ve moved. If you have the means and the connections, at least one of these addresses should be in another country, under the care of a nominee who can check the mail and forward mail to you as needed.
- Sell Your Vehicles and Buy New Ones – Buy new vehicles in the name of LLCs and register your new vehicles with the state you will be driving them in, but register them in the name of LLCs, using ghost addresses in distant states or countries.
- Use an Alternate Name – Frank Ahern is a former skip tracer who writes that it’s simple to find most people if you know their legal name. All you need is a prepaid cellphone and a prepaid credit card. Then just hop on line and pay for an online search. After you move, introduce yourself to your neighbors and local businesses using an alternate name. If you get caught, explain to them that you are a writer and need to protect your identity. If you took my advice about becoming a citizen journalist, you’ll be telling the truth. If someone looking for you suspects you are in an area, they’ll call around to local businesses someone like yourself is likely to have used.
Destroy Unneeded Documents Containing Sensitive Information
Destroying sensitive documents that are no longer needed reduces the risk that the information they contain will be compromised. It also frees up space and reduces clutter.
Methods of Document Destruction
- Shredding/Milling (Dry Process) – Don’t rely on standard strip or crosscut shredders along. There have been numerous cases where shredded documents have been reconstructed. At minimum, use an NSA/CSS-approved micro-cut shredder. They cut a document into both more and smaller pieces that strip or cross-cut shredders. Government agencies allowed to use shredders for document destruction then pass shredded material through a security screen to ensure the bits are small enough that classified information cannot be disclosed.
- Incineration – Use a home incinerator that is made to withstand the elements and has plenty of ventilation. If you intend to shred before incineration, a home incinerator would need to have screen installed to prevent shredded material from being carried away by the wind.
- Pulping (Wet Process) – Pulping requires water, a large water-tight tub or trash can and an agitator such as drill with a paint mixer attachment. Material must be water soluble. Add material to a large tub or bucket. Add plenty of water, making sure that the paper is completely covered and then let it sit for a day. Then agitate the material thoroughly with an electric drill fitted with a paint mixer. The paper will resemble oatmeal once pulped. If you like, press the pulp to remove the water and dry pellets, bricks or “logs” to burn instead of wood.
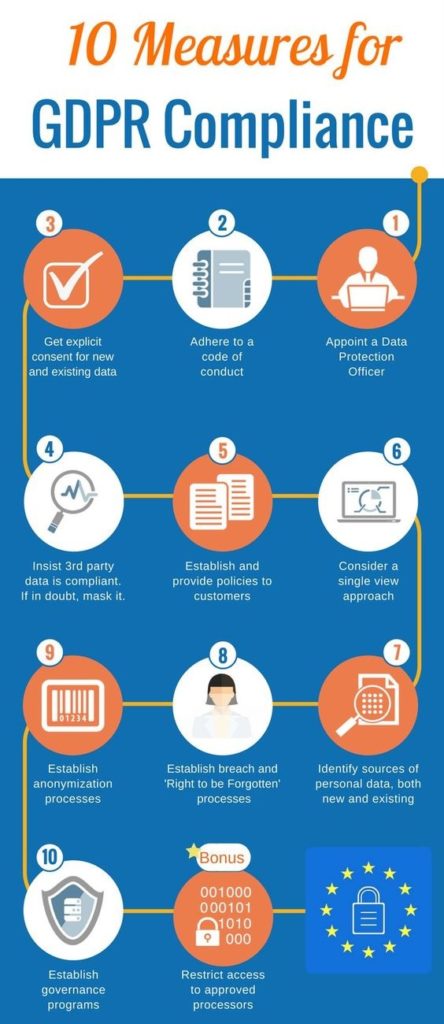
Use Privacy Companies
Privacy companies offer services to consumers who value privacy. These services include
- Masked Phone Numbers – The company gives you a phone number in the area code of your choice. People call that number and the calls are forwarded to your phone. You can block numbers you don’t want to hear from with one click and they just hear a “no service” message.
- Masked Credit Cards – The service creates a credit card good for only one transaction in an amount that you specify. This is a secure way to deal with sketchy online vendors without giving them any information from your bank accounts, protecting you from identity theft.
- Masked Text Messages – Enables you to send and receive text messages from a masked phone number.
- Spoofing Cards – Enables you to specify what caller ID information is shown to the phone receiving the call.
- Mail Forwarding & Scanning – Mail services scan your mail and email you images of the scans. They will open mail for you and send you scan, destroy it or mail it to someplace you specify, at your option.
- Pre-paid Phones – Pre-paid phones are cheap and easy to use and offer far more privacy than using a major carrier. It seems phone providers are out to steal your data anyway they can. Sometimes you just need to make a phone call and don’t need a bunch of bells and whistles that just run the battery down or you’re traveling somewhere you are likely to be robbed and you don’t want to risk losing a $1,000 phone.
- Pre-paid Credit Cards – Some vendors don’t take cash and pre-paid cards can in situations where you need something from an online vendor but don’t want it traced back to you.
Use Your Passport for ID
When asked for ID, show your passport. The reason is that it doesn’t have your address on it. There is a place to pencil in an address but doing so only gives out more information than necessary. The types of folks you may want to hide from can’t do much with a passport number and if it’s a government that’s after you, you’ll need to read more than a few articles online.
Family & Friends
Family can be one of the toughest areas to get handle on, but anyone you stay in touch with needs to respect your need for privacy. If it is important to find you whoever is on your trail will go through yearbooks at your high school and college to hunt down old friends to see if you stay in touch. If you have kids, they’ll contact their schools and lie to get information about where their records went. If you want to protect the privacy of you children, the only options are private schools or homeschooling. The types of people who do this work believe that you must have done something to deserve to be hunted down so if it means taking advantage of children or the elderly to find you, don’t expect a sense of right and wrong to stop them.
Opt Out & Seed Disinformation
The primary motivation of data clearinghouses is profit and consumer data is big business. This presents a problem to consumers who value their privacy. In the course of life, the average person creates too many online accounts to remember a unique secure password for each one, thoroughly read the user agreement and jump through all the hoops required to opt out of data collection. Data clearinghouses count on it. There are two things you can do to reduce your If this describes your situation: opt out and misinform.
There are several books on privacy that include lists of where to go to opt out of data clearinghouses and even some automated methods of doing just that. It takes a lot of work, but if you are serious about reducing your online footprint, buy a couple and set to work.
Even with automated services that it is difficult to get some lists to remove your information, but even if you can’t remove it, you may be able to “correct” information. Changing addresses, dates or even a single letter in a name can throw nationwide searches off your track. The idea is to investigate yourself. Go to the same sites and records those that come after you will surely check and make sure that what they find doesn’t lead to you. Create alerts with DuckDuckGo to let you know when new information about you or your addresses appears online. Just make sure that the emails they notify are dead ends. In the process, you’ll learn a great deal about how they work and how to avoid them.



































































Because of the drug epidemic, many landlords now refuse prepaid leases.
Any alternatives to passports? My privacy invaders belong to an extended family which essentially “owns” the postal workers’ union.
Other than these two items, Cache’s advice is spot-on. I caught one of their crooks this week because he showed up in two sites where he was a demographic outlier. Oddly enough, he avoided two more shops where he would have been the only male, proving he was sexist and demographically egoistic.
Just printed out all four episodes of your article.. I’m guessing that it’s going to tell me that I shouldn’t be contacting you to tell you that I appreciate your putting this together, but what the hey. I’m looking forward to reading the entire thing, but just in case I become paranoid in the process, I thought it best to let you know that it is being read and evaluated by someone and appreciated by many more.
Thank you very much for your message, Robert. Have a good read and stay safe!
Alex from Survivopedia 🙂